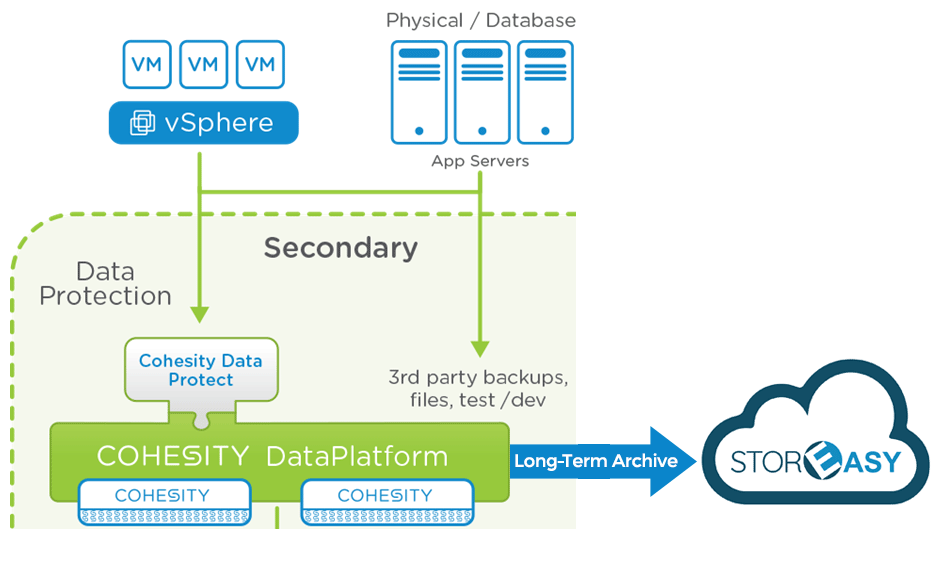
L’innovativa tecnologia DataProtect sviluppata da Cohesity si basa su una potente e flessibile architettura iperconvergente in grado di proteggere gli ambienti fisici e virtuali, i database e le applicazioni, in un’unica soluzione allo stato dell’arte, orientata alle applicazioni, che si estende dalle infrastrutture On Premise al Cloud
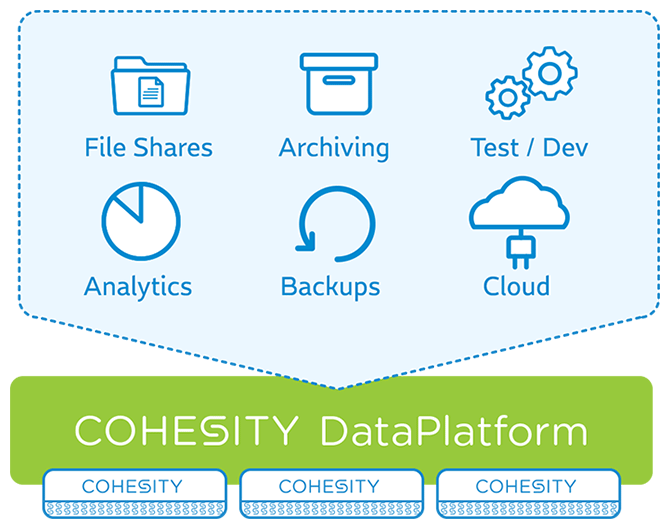
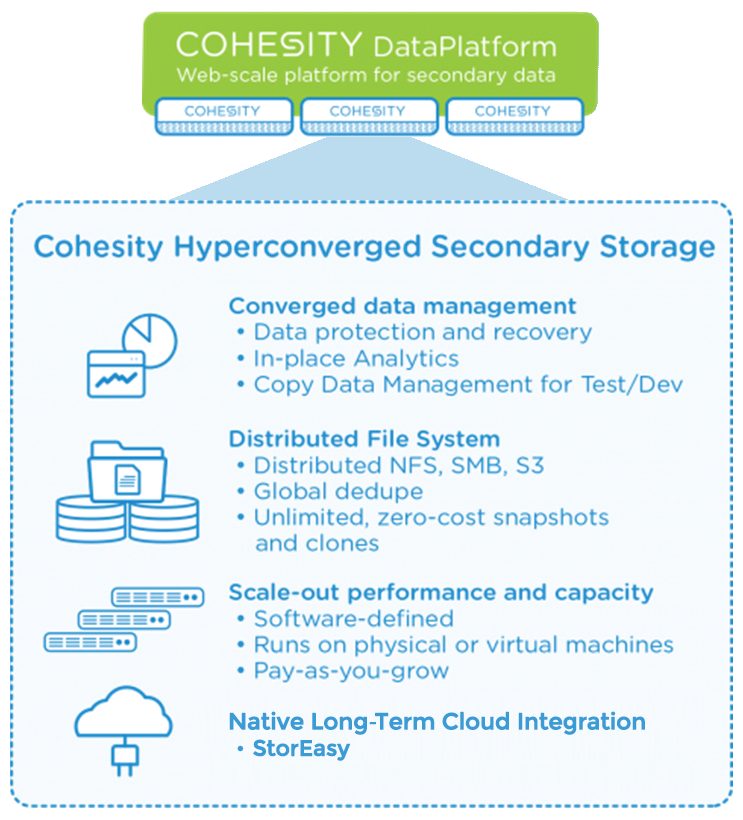
Cohesity ha sviluppato un’architettura innovativa in grado di consolidare i tradizionali silos di storage come il software di backup, la deduplica dei dati, file storage e cloud gateway all’interno di una singola piattaforma scale-out in grado di creare un ambiente semplice da gestire, efficiente e scalabile.
A differenza di altre soluzioni che utilizzano il backup come risorsa primaria, la tecnologia DataProtect è in grado di creare cloni di qualunque tipologia di dati (backup, file, oggetti) su larga scala, in qualunque momento, senza influire sulle prestazioni. I dati sono presentati in modalità NFS / SMB / S3 senza restrizioni e con alte prestazioni per permettere agli applicativi di utilizzare i dati trasparentemente senza apportare modifiche al modo di operare.
StorEasy è il primo Cloud Storage Provider in grado di garantire un’integrazione nativa con la soluzione DataProtect per l’erogazione di servizi Long-Term Archive attraverso una piattaforma Active Archive certificata da Cohesity
Per gestire all’interno di StorEasy l’archiviazione di lungo periodo per l’innovativa piattaforma Cohesity DataProtect è stata sviluppata una sofisticata architettura Active Archive basata su tecnologia nastro LTO.
Lo scopo di un ambiente Active Archive è di rendere tutti i contenuti online o near-online (nel caso delle librerie nastro) utilizzando storage a basso costo. Un’architettura ibrida che utilizza differenti tier storage per garantire elevate prestazione e costi di esercizio estremamente ridotti rispetto alle tradizionali architetture basate prevalentemente da dischi magnetici.
I nastri, e in particolare la tecnologia LTO, è oggi non solo conveniente economicamente per realizzare una seconda o una terza copia di sicurezza, ma offre altresì un’affidabilità straordinaria, un error rate 10.000 volte inferiore rispetto ad un disco SATA e una leggibilità dei dati memorizzati sui supporti LTO garantita per un periodo di 30 anni.
La soluzione Active Archive include il caching dei dati sia per la fase di scrittura, sia per quella di lettura, in pratica, una percentuale dei i dati archiviati al suo interno permane in doppia copia anche sulla cache. La permanenza dei dati all’interno della cache è determinata da specifiche policy programmabili che permettono di terminare dinamicamente quali e quanti dati mantenere al suo interno.
Questa modalità consente un’immediatamente lettura dei dati senza dover accedere direttamente ai nastri presenti nelle librerie nastro, comprensibilmente la dimensione della cache deve essere opportunamente dimensionata per mantenere in linea solo quei dati che per una specifica ragione operativa dovranno essere acceduti all’interno di un determinato lasso di tempo. La permanenza dei dati nei dischi che compongono la cache e i relativi parametri di soglia sono programmabili dinamicamente, qualora il livello dovesse essere superato, la cache viene liberata dai file meno acceduti (sui nastri ovviamente sono già archiviati tutti i dati indipendentemente da quello che avviene all’interno della cache).
Archiviazione di lungo periodo per Cohesity DataProtect
Tecnologia nastro LTO/LTFS
Come sappiamo i nastri LTO offrono una tecnologia sicura, affidabile ed economica, in grado di archiviare le informazioni per un arco di tempo che può estendersi per decenni, una memoria “elastica” che può essere utilizzata per memorizzare quantità illimitate di dati in modo estremamente sicuro ad una frazione del costo rispetto a qualsiasi altra tecnologia storage oggi presente sul mercato. I nastri LTO sono offrono un error rate 10.000 volte inferiore di un disco SATA, mentre la leggibilità e garantita per un periodo di 30 anni, supportano un milione di passaggi e 20.000 cicli di scrittura per singolo LTO, un MTBF (Leading Mean-Time-Between-Failure) di 250.000 ore con duty cycle del 100%. Senza dimenticare che un singolo tape LTO-8 offre una capacità nativa di 12 TB e 30 TB compressi.Linear Tape File System (LTFS)
L’aumento di popolarità delle architetture Active Archive basato su nastro è principalmente dovuto alla diffusione del formato Linear Tape File System (LTFS) conforme allo standard ISO/IEC 20919:2016.
L’aspetto più rilevante delle standard LTFS è la possibilità di trasportare i media registrati tra differenti sistemi operativi, applicazioni e piattaforme che adottano questo formato, consentendo di utilizzare il nastro come se fosse un tradizionale hard disk (volume standard con directory e sottodirectory).
Regolamento Generale sulla Protezione dei Dati (GDPR)
 La protezione Long-Term Archive offerta da StorEasy è in linea con il Regolamento Generale sulla Protezione dei Dati (GDPR) e per tutte quelle applicazioni e normative che richiedono un’archiviazione sicura per periodi estremamente lunghi come ad esempio i documenti legali, contabili e amministrativi che per obbligo di legge devono essere archiviati per un periodo di 10 anni, altri documenti per intervalli molto più lunghi, alcuni anche indefinitamente.
La protezione Long-Term Archive offerta da StorEasy è in linea con il Regolamento Generale sulla Protezione dei Dati (GDPR) e per tutte quelle applicazioni e normative che richiedono un’archiviazione sicura per periodi estremamente lunghi come ad esempio i documenti legali, contabili e amministrativi che per obbligo di legge devono essere archiviati per un periodo di 10 anni, altri documenti per intervalli molto più lunghi, alcuni anche indefinitamente.
Archiviazione Long-Term Archive in modalità WORM (Write Once – Read Many)
La tecnologia WORM permette di archiviare i dati in modo non-riscrivibile e non-cancellabile; applicando questa tecnica i dati registrati non potranno più essere sovrascritti, modificati e/o manipolati. Il processo di protezione WORM offerto da StorEasy per l’archiviazione di lungo periodo è aderente alla più stringenti normative nazionali e internazionali nell’ambito dell’archiviazione dei dati sensibili, dematerializzazione dei documenti, archiviazione sostitutiva e archiviazione dei file log. La soluzione garantisce la tenuta nel tempo sicura ed opponibile verso terzi dei dati archiviati grazie alla piena aderenza ai requisiti di conformità richiesti dalla legge.
Data at Rest Encryption per i dati archiviati sui media LTO
Il servizio Long-Term Archive impiega l’Advanced Encryption Standard (AES), uno degli algoritmi di crittografia più utilizzati e sicuri disponibili sul mercato, non esiste nessun attacco praticabile contro AES, non a caso è lo standard di crittografia preferito da governi, banche e sistemi di alta sicurezza in tutto il mondo. Attraverso la crittografia i media LTO potranno essere letti solo da chi possiede la chiave corretta per decodificarle. I dati sono crittografati direttamente dalle unità nastro LTO con chiave AES-256, questa operazione viene effettuata da un hardware specializzato presente all’interno dei drive alloggiati all’interno delle librerie nastro.
Tecnologia Secure Hash Algorithm (SHA) per il controllo dell’integrità dei dati archiviati
In aggiunta alla garanzia dei produttori dei media che garantiscono la leggibilità dei dati per un periodo di 30 anni, StorEasy ha introdotto ulteriori livelli di controllo per l’integrità dei dati registrati sui nastri LTO.
Per garantire la leggibilità dell’archivio anche nel caso di danneggiamenti, usura e potenziali corruzioni dei supporti magnetici, vengono effettuate operazioni di scansione periodica per il controllo dell’integrità dei supporti (media LTO) allocati all’interno delle librerie nastro attraverso la lettura di specifici dati di controllo inseriti all’atto della scrittura degli stessi.
Il controllo dell’integrità dei dati è realizzato attraverso la funzione hash, un algoritmo che in funzione di una quantità di dati arbitraria in ingresso, genera in uscita un output di lunghezza predefinita, generando così un “impronta” dei dati d’ingresso. Questa operazione viene effettuata per ogni file archiviato, l’hash determinato dall’operazione Secure Hash Algorithm (SHA) viene memorizzata insieme al file. Gli hash sono ricalcolati e confrontati nel corso delle scansioni programmate per il controllo dell’integrità dei media. Se un hash non dovesse apparire corretto durante la verifica, il file associato sarà contrassegnato come “bad”. In tal modo sarà recuperata un’altra copia del file (copia di sicurezza off-line) in sostituzione di quello corrotto al fine di reintegrare il corretto numero di copie. Conseguentemente verrà effettuata la seconda (o la terza copia) del file su un nuovo media.

